NEWS, EVENTS & BLOG
BLOG
The Best SBC for Secure Embedded Systems – Part 1
Press Office, VersaLogic Corporation, 11/18/20
Part 1: Securing My Embedded Computing System, Should I Care?
Ensuring that embedded systems are secure has become important in almost every type of application. The obvious ones are medical, financial, defense, communications, transportation, and power grid systems. But in addition, with the wide-spread deployment of IoT in factory automation, building security systems, and smart city functions, the need for secure embedded computing systems is ever increasing. The consequences of a data breach or a system take-over can be severe, including:
- Financial loss
- Breach of HIPAA regulations
- National security impacts
- Damage to communications and power systems
- Factory down-time
- Etc.
[video width="680" height="auto" mp4="https://www.versalogic.com/wp-content/uploads/2020/11/Best_SBC_for_Secure_Embedded_Systems-v2.mp4"][/video]
How Can Embedded Systems Be Secured?
Security measures can take many forms. Some are processor-based, and others, such as Trusted Platform Module (TPM) rely on hardware measures external to the processor. In addition, there is remote access to be considered as well as the use of physical security methods. We’ll focus only on the processor-based measures in this blog entry.Processor-Based Security Measures
Encryption is at the heart of much processor-based security. Many processors support the Advanced Encryption Standard (AES). AES originated in 2001 in Federal Information Processing Standards Publication 197 (FIPS PUB 197). The AES algorithm enables fast and secure encryption and decryption and utilizes cryptographic keys up to 256 bits in length. AES is implemented in X86 and Arm®-based processors. Intel, who started shipping products with what they called Intel® Advanced Encryption Standard (AES) New Instructions Set (Intel® AES-NI) in 2010, has a white paper containing extensive details about how AES works.Keys to the Kingdom
If you’ll pardon the pun, the key to secure encryption relies on having randomly generated secure keys. Amongst other things, FIPS PUB 140 defines a standard for cryptographic key management. Intel processors support this through Intel® Secure Key which is a set of instructions and an underlying hardware implementation of a digital random number generator that meets FIPS PUB 140 and other standards such as NIST’s SP 800-90A.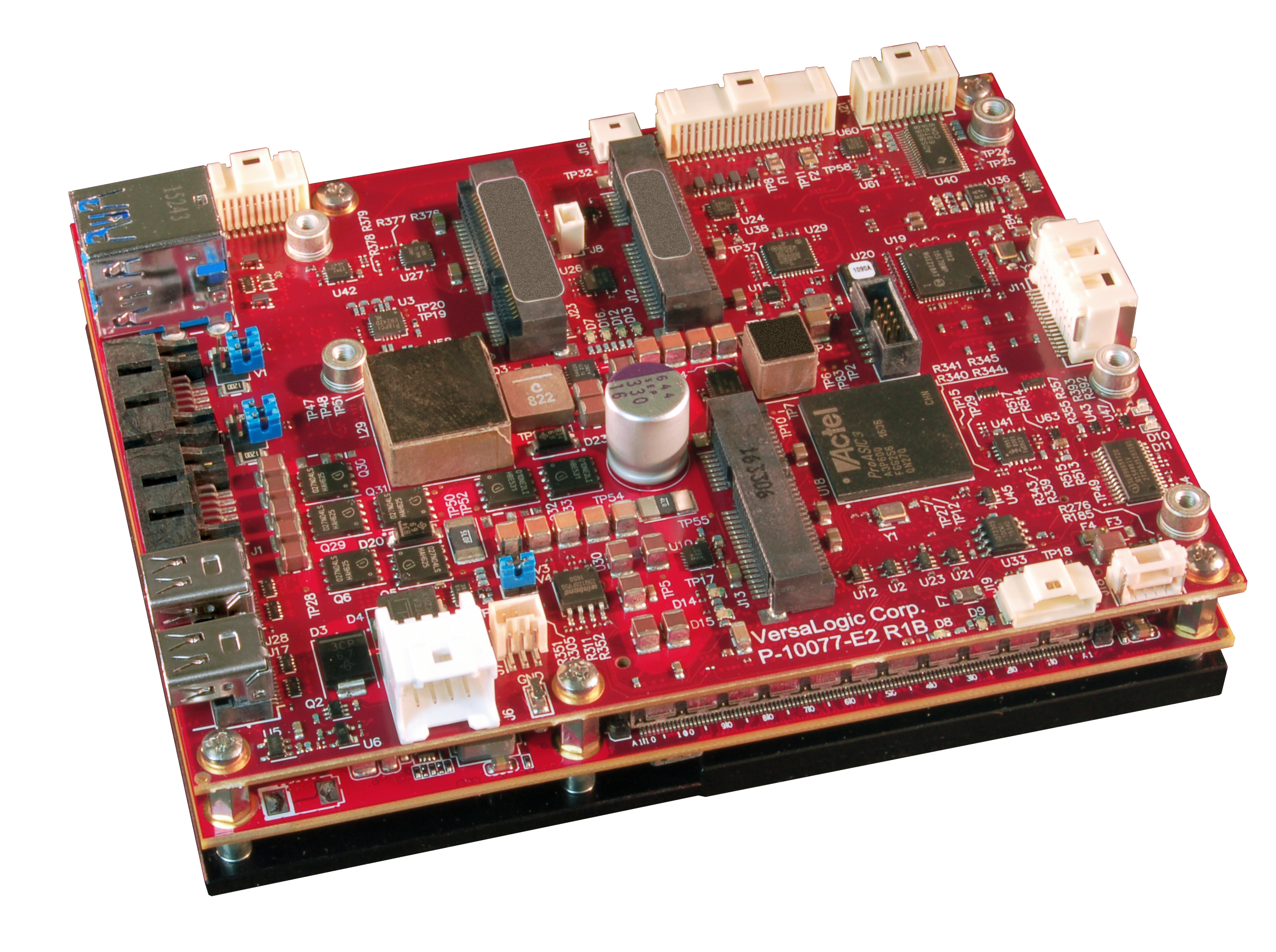
VersaLogic’s EPU-4562, Blackbird, features the Intel® Core™ i7-6822EQ Processor with AES-NI and Secure Key technology
Speeding Up Encryption and Decryption
When dealing with large amounts of data, such as in high performance edge compute (HPEC) and edge server applications, it’s necessary to perform encryption and decryption quickly. Intel features Intel® QuickAssist Technology in its C3000 Atom™ server-grade processors. This offloads the encryption and decryption tasks from the main processor cores and provides cryptography services at speeds up to 20 Gbps.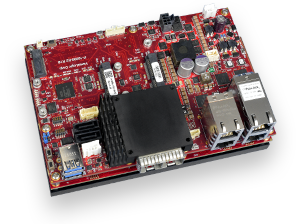
Designed and built for edge server and HPEC application in tough environments at the edge, VersaLogic’s ”Grizzly” has 10 GbE SFP+ ports, 16-core compute capabilities, and features Intel® AES-NI, Secure Key and Quick Assist Technology
Boot-Time and Execution Protection
In addition to encrypting data, there are other security measures to consider. One of these is to resist attacks and infection from malware. Secure Boot, which is defined in the Unified Extensible Firmware Interface (UEFI) specifications, is an interface between the OS and the platform firmware /BIOS. It relies on a chain of trust based on a number of keys and databases:- The Platform Key (PK) relates to a trust relationship between the platform owner and the UEFI BIOS.
- The Key Exchange Key (KEK) database is responsible for a trust relationship between the BIOS and the operating system. The private portion of the PK must be used to modify this database.
- Security database (db) contains signatures of UEFI images that may be loaded.
- Security database (dbx) is a blacklist of images that may not be loaded. Again, this database can always be read, but the private portion of an enrolled KEK or the private portion of the PK must be used to write to this database.
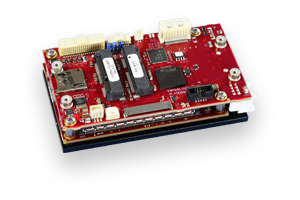
The SWaP-optimized "Harrier", features the Apollo Lake E3900 series of processors which includes both Secure Boot and Execute Disable technology
This blog entry has mainly focused on x86 architecture, however, Arm®-based processors also include a range of security measures such as the Arm® TrustZone® technology incorporated into the Arm® Cortex®-A architecture used in processors such as NXP’s i.MX6 family.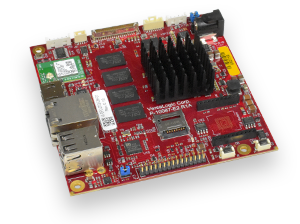
The wireless-equipped “Swordtail”, uses NXP’s i.MX6 SOCs featuring TrustZone® technology
That’s a start to the security story. Look out for the next pieces in the security blog series on Trusted Platform technology, remote access considerations, and physical security.